Cyberdefenders – FakeGPT Lab writeup
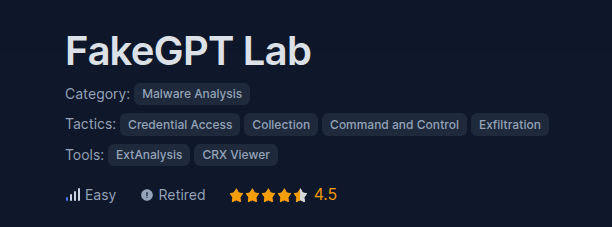
Instructions: Uncompress the lab (pass: cyberdefenders.org) Scenario: Your cybersecurity team has been alerted to suspicious activity on y
Instructions: Uncompress the lab (pass: cyberdefenders.org) Scenario: Your cybersecurity team has been alerted to suspicious activity on y
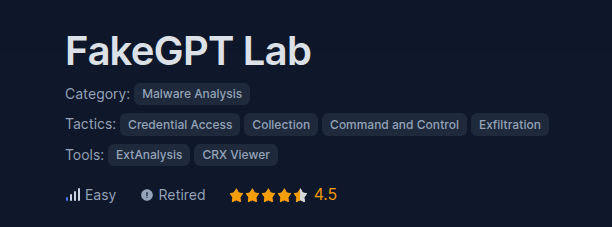
Instructions: Uncompress the lab (pass: cyberdefenders.org) Scenario: A large multinational corporation heavily relies on the 3CX software
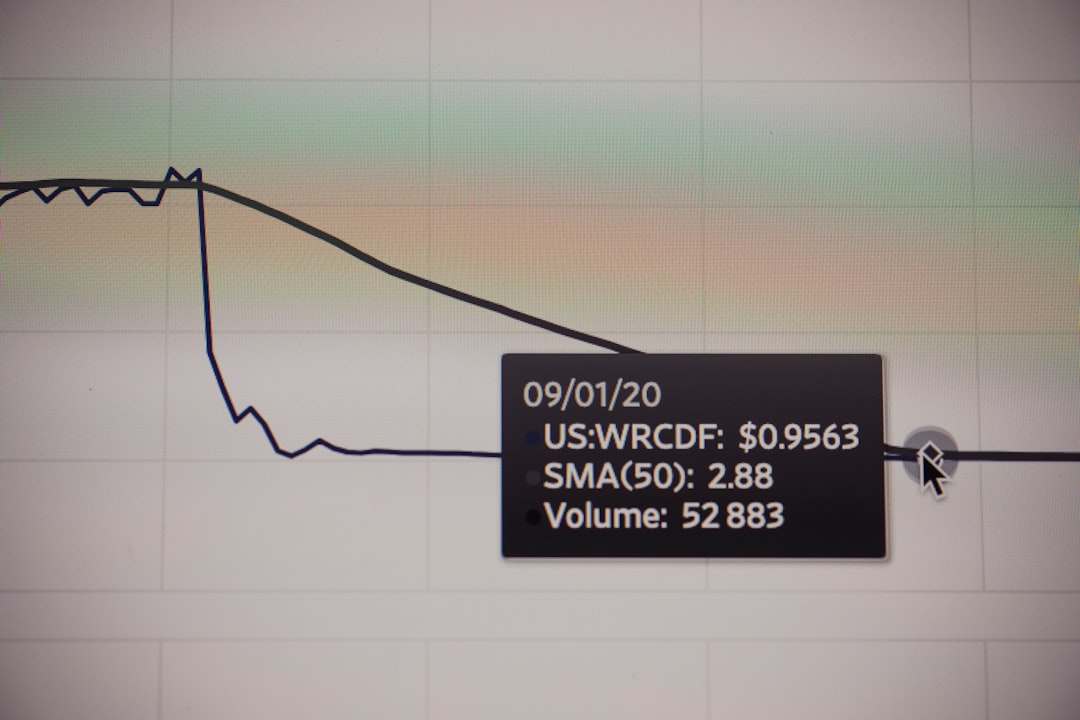
Instructions: Uncompress the lab (pass: cyberdefenders.org) Scenario: As a cybersecurity analyst for a leading financial institution, an a
Instructions: Uncompress the lab (pass: cyberdefenders.org) Scenario: You are part of the Threat Intelligence team in the SOC (Security Op
Instructions: Uncompress the lab (pass: cyberdefenders.org) Scenario: Our intrusion detection system has alerted us to suspicious behavior
Scenario: As a member of the Security Blue team, your assignment is to analyze a memory dump using Redline and Volatility tools. Your goal i
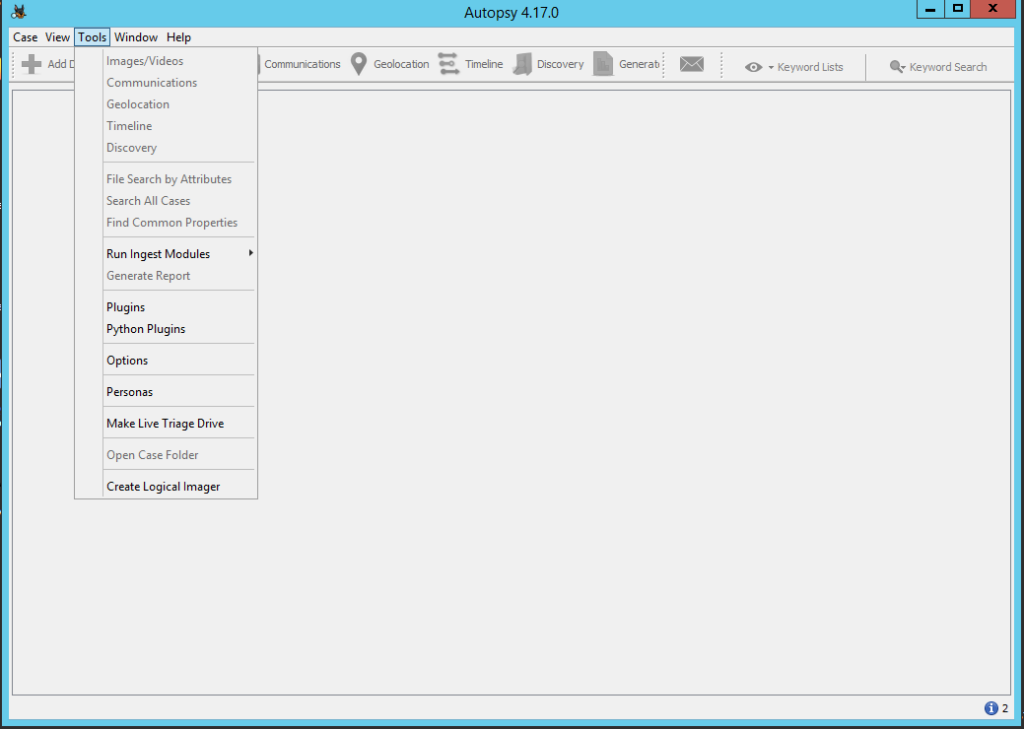
Introducción En el mundo de la informática forense, disponer de herramientas robustas y eficientes es fundamental para realizar análisis pre
Introducción En el ámbito de la respuesta a incidentes y el análisis forense digital, el análisis de la memoria es una herramienta crucial p

Scenario: During your shift as a tier-2 SOC analyst, you receive an escalation from a tier-1 analyst regarding a public-facing server. This

Scenario: An attacker was able to trick an employee into downloading a suspicious file and running it. The attacker compromised the system,

Seguimos con la seríe de Emulación de ataques mediante Atomic Red Team y Detección con Azure Sentinel Parte. Ver parte 1, Ver parte 2, Ver p