En primer lugar, como requisito previo es necesario registrar una nueva app en Azure AD y crear un Client Secret.
Los datos que necesitaremos para la configuración son los siguientes:
- Application (client) ID
- Directory (tenant) ID
- Client Secret ID
*NOTA: Para llevar acabo esta configuración es necesario tener licencia Enterprise.
Para poder llevar acabo la configuración en Elastic tenemos que crear la siguiente keystore
/usr/share/elasticsearch/bin/elasticsearch-keystore add xpack.security.authc.realms.oidc.cloud-oidc.rp.client_secret
warning: ignoring JAVA_HOME=/usr/lib/jvm/java-11-openjdk-amd64; using bundled JDK
Enter value for xpack.security.authc.realms.oidc.cloud-oidc.rp.client_secret:Agregamos la siguiente configuracion en /etc/elasticsearch/elasticsearch.yml
xpack.security.authc.token.enabled: true
xpack:
security:
authc:
realms:
oidc:
cloud-oidc:
order: 2
rp.client_id: "<CLIENT ID>"
rp.client_secret: "<CLIENT SECRET ID>"
rp.response_type: code
rp.redirect_uri: "https://red-orbita.com:5601/api/security/v1/oidc"
op.issuer: ""https://login.microsoftonline.com/<DIRECTORY TENANT ID>/v2.0"
op.authorization_endpoint: "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/oauth2/v2.0/authorize"
op.token_endpoint: "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/oauth2/v2.0/token"
op.jwkset_path: "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/discovery/v2.0/keys"
op.userinfo_endpoint: "https://graph.microsoft.com/oidc/userinfo"
op.endsession_endpoint: "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/oauth2/v2.0/logout"
rp.post_logout_redirect_uri: "https://red-orbita.com:5601/logged_out"
claims.principal: subEsta información la podemos obtener ejecutando la siguiente consulta
curl https://login.microsoftonline.com/<DIRECTORY TENANT_ID>/v2.0/.well-known/openid-configuration | jq
Salida del comando:
{
"token_endpoint": "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/oauth2/v2.0/token",
"token_endpoint_auth_methods_supported": [
"client_secret_post",
"private_key_jwt",
"client_secret_basic"
],
"jwks_uri": "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/discovery/v2.0/keys",
"response_modes_supported": [
"query",
"fragment",
"form_post"
],
"subject_types_supported": [
"pairwise"
],
"id_token_signing_alg_values_supported": [
"RS256"
],
"response_types_supported": [
"code",
"id_token",
"code id_token",
"id_token token"
],
"scopes_supported": [
"openid",
"profile",
"email",
"offline_access"
],
"issuer": "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/v2.0",
"request_uri_parameter_supported": false,
"userinfo_endpoint": "https://graph.microsoft.com/oidc/userinfo",
"authorization_endpoint": "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/oauth2/v2.0/authorize",
"device_authorization_endpoint": "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/oauth2/v2.0/devicecode",
"http_logout_supported": true,
"frontchannel_logout_supported": true,
"end_session_endpoint": "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/oauth2/v2.0/logout",
"claims_supported": [
"sub",
"iss",
"cloud_instance_name",
"cloud_instance_host_name",
"cloud_graph_host_name",
"msgraph_host",
"aud",
"exp",
"iat",
"auth_time",
"acr",
"nonce",
"preferred_username",
"name",
"tid",
"ver",
"at_hash",
"c_hash",
"email"
],
"kerberos_endpoint": "https://login.microsoftonline.com/<DIRECTORY TENANT ID>/kerberos",
"tenant_region_scope": "EU",
"cloud_instance_name": "microsoftonline.com",
"cloud_graph_host_name": "graph.windows.net",
"msgraph_host": "graph.microsoft.com",
"rbac_url": "https://pas.windows.net"
}Creamos el rol en Elastic
curl --user elastic --insecure -X PUT 'https://localhost:9200/_security/role_mapping/oidc-kibana' -H 'Content-Type: application/json' -d '
> {
> "roles": [ "kibana_user" ],
> "enabled": true,
> "rules": {
> "field": { "realm.name": "cloud-oidc" }
> }
> }'
Enter host password for user 'elastic':
{"role_mapping":{"created":true}}Por ultimo agregamos la siguiente configuración a kibana: /etc/kibana/kibana.yml
xpack.security.authc.providers:
oidc.oidc1:
order: 0
realm: cloud-oidc
description: "Log in with Azure AD"
basic.basic1:
order: 1
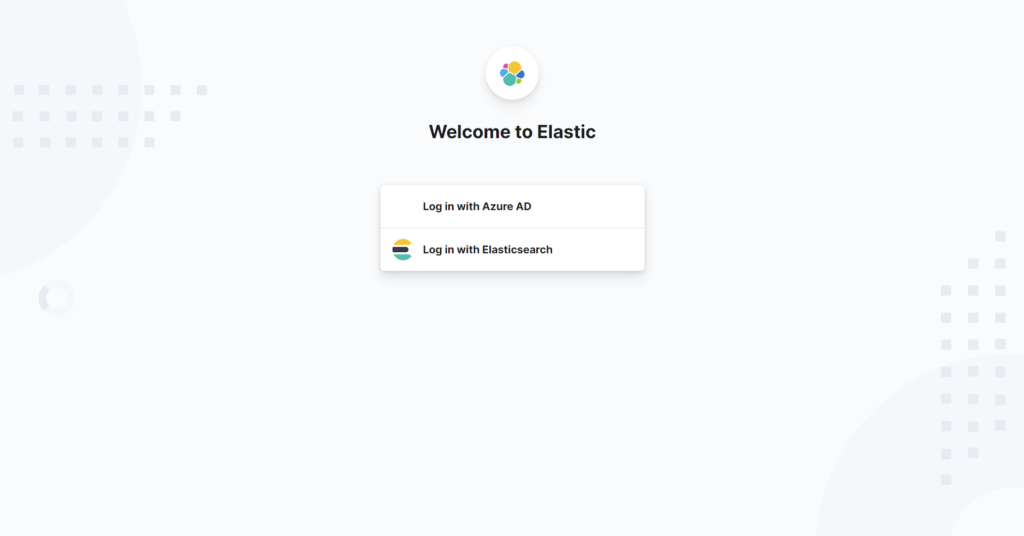
:wq!